Authorization Pipeline
End-to-end authorization workflow with automated security scanning, SBOM generation, compliance checks, and multi-stakeholder approval chain.
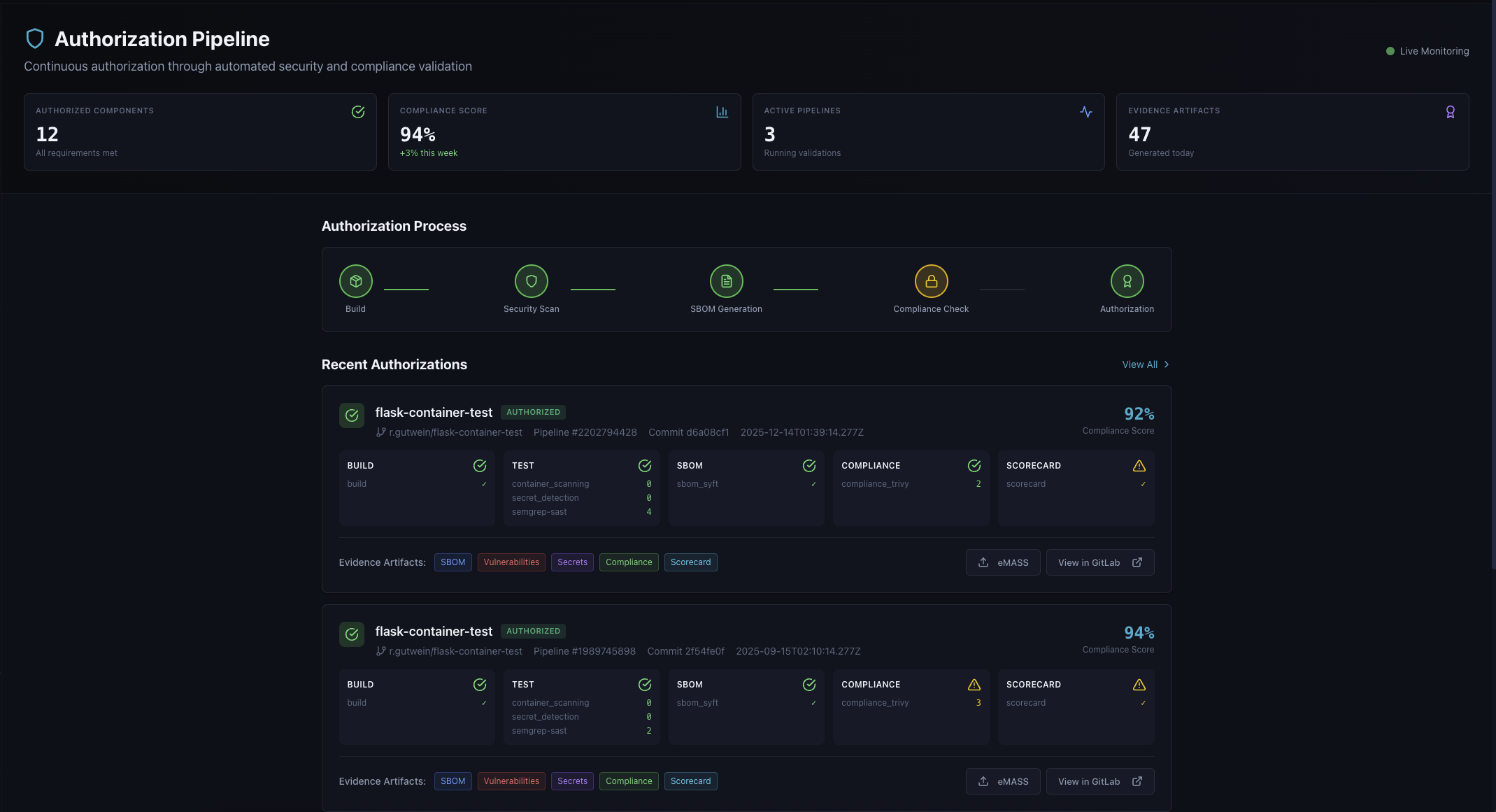
Authorization pipeline showing Build, Security Scan, SBOM Generation, Compliance Check, and Authorization stages with SCA, ISSO, ISSM, and AO approval workflow