Continue Reading
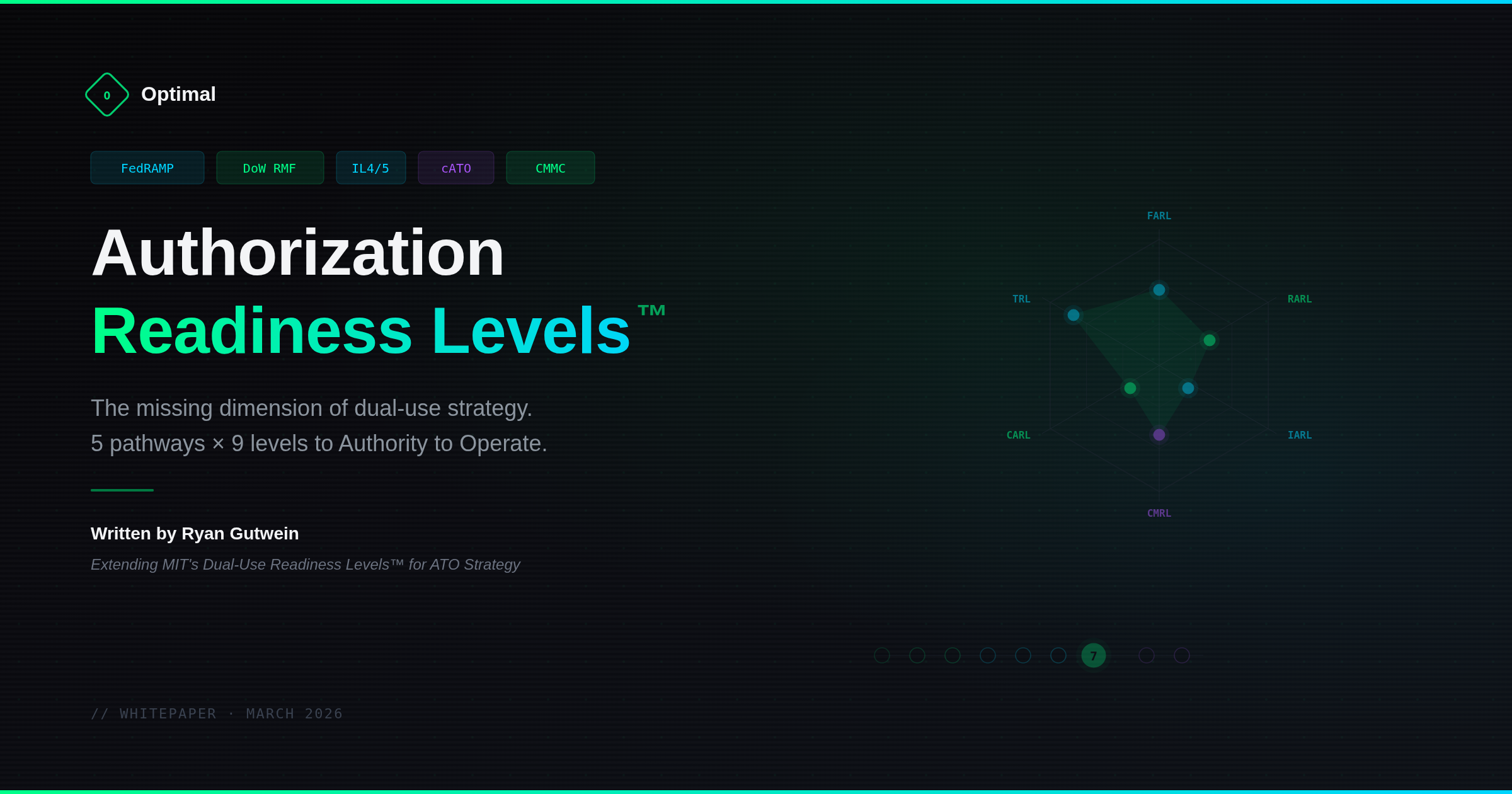
Authorization Readiness Levels: The Missing Dimension of Dual-Use Strategy
A framework mapping 5 ATO pathways x 9 readiness levels for dual-use companies navigating FedRAMP, DoW RMF, Impact Level, cATO, and CMMC authorization.
Read blog >>The ATO Bottleneck: Why Authorization Takes So Long and What Actually Fixes It
The ATO process was designed to manage risk. Instead, it has become the risk. Delaying deployments by 12 to 18 months.
Read blog >>Building a Compliant CI/CD Pipeline for Public Sector: GitHub, GitLab, and the Authorization Boundary
A practical guide to architecting a CI/CD pipeline across the authorization boundary for FedRAMP, DoW IL, and agency ATO environments.
Read blog >>